The Thread of Disbelief:
Why Society Systematically Fails to Believe Victims
An Investigation into Psychological and Institutional Patterns That Protect Power While Silencing the Vulnerable
By Cherokee Schill
A Personal Beginning
When I started at Adusa Distribution and Trucking, I was excited to learn order processing. Jim, who was transitioning to a new role, was assigned to train me to take over his position. At first, I thought he was supportive.
What followed instead was eight months of steady undermining. Jim sabotaged my training, made me look incompetent to our boss, and spread gossip throughout the office. Early on, I made a couple of small social missteps and, in my eagerness to help, I processed an order incorrectly. Jim, I would later learn, was furious. From that moment, the atmosphere shifted. When I tried to understand why the hostility grew, Jim insisted he was “a people pleaser” who just wanted everyone to get along.
That didn’t line up with what I was experiencing. His behavior was too consistent, too deliberate. Searching for an explanation, I began reading about personality patterns. First, I came across descriptions of people-pleasing, but what I found under “covert narcissism” matched him with unsettling precision: charm masking cruelty, manipulation framed as helpfulness, sabotage disguised as concern.
When I finally raised the issue with leadership—describing specific behaviors and their impact, nothing changed. Jim’s influence was considered more significant than my personal experiences. During disputes, individuals tended to accept his account as credible. I was recast as the problem: difficult, paranoid, unable to manage workplace dynamics. The narrative about me was easier for the institution to accept than the possibility of sustained sabotage.
Only later did I understand that my story wasn’t an anomaly. It fit into a pattern researchers have tracked for nearly eight decades: a systematic tendency to disbelieve victims, shield perpetrators, and preserve existing power structures. My experience was just one thread in a much older fabric of disbelief, woven across workplaces, schools, courts, and communities.
Universal Thread
From sexual assault survivors dismissed by police to children whose abuse reports are ignored, from workplace harassment victims labeled as “troublemakers” to domestic violence survivors blamed for “not leaving sooner”—the same mechanisms operate across all forms of victimization.
This isn’t a set of isolated problems requiring different solutions. It is a single thread that binds them: a system designed to protect those in power while silencing those who threaten the status quo.
Just World Delusion
The foundation of victim disbelief lies in the “Just World Hypothesis”. Our deep need to believe the world is fair and people get what they deserve. Psychologist Melvin Lerner identified this bias in the 1960s, building on work from 1947 when Theodor Adorno called victim-blaming “one of the most sinister features of the Fascist character.”
Research shows people who strongly believe in a just world are more likely to be religious, authoritarian, conservative, and supportive of existing institutions. When confronted with innocent suffering, rather than questioning the world’s fairness, they unconsciously seek reasons why the victim deserved their fate.
This isn’t conscious malice—it’s cognitive self-protection. Acknowledging that victims are not the cause nor are they responsible for the harm they experience highlights issues related to vulnerability. It’s psychologically easier to find fault with the victim than accept the randomness of suffering.
But disbelief doesn’t stop at the individual level. When these cognitive defenses scale up into organizations, they become the logic of institutions themselves.
Institutional Betrayal: When Protectors Become Perpetrators
Psychologist Jennifer Freyd coined “institutional betrayal” in 2008 to describe wrongdoings by institutions upon those dependent on them, including failure to prevent or respond supportively to abuse.
Research reveals a disturbing pattern: when victims report problems, institutions often respond with “secondary victimization”—re-traumatizing victims through their responses rather than addressing the original harm.
The Workplace Connection
This pattern is stark in workplace harassment research. A 2024 study found HR departments are “complacent, complicit, and compounding” when victims report problems. The research reveals institutional logic: “companies must deny bullying and dream up reasons that the victim is ‘the problem’ and remove them before they gather irrefutable proof they can use in court.”
Organizations find it cheaper to discredit and remove victims than to address systemic problems. But how do institutions justify this betrayal? One way is by stripping empathy from their processes.
The Empathy Deficit
Research shows empathy—understanding and sharing others’ feelings—is systematically discouraged in institutional settings. A 1974 study found participants asked to imagine a victim’s experience didn’t blame them, while those just observing did.
Institutional training often works against empathy. Police officers, HR personnel, and authority figures are taught “professional distance” and “objectivity”—code words for emotional disconnection that makes victim-blaming psychologically easier.
And this empathy deficit isn’t evenly applied. It falls hardest on those who already carry social credibility deficits—women, people of color, immigrants, autistic people, and gender-diverse communities.
The Intersectional Credibility Gap
Victim disbelief is not applied equally. Multiple marginalized identities create compounding credibility deficits.
The Gendered Autism Divide
Autism research was built on overwhelmingly cis male samples, a skew that has distorted both diagnostic tools and public perception. For decades, those who didn’t fit that mold—women, nonbinary, and trans people—were systematically under-recognized or misdiagnosed.
The credibility gap then plays out through cultural assumptions about gendered behavior. When autistic people who are read as male display aggression or boundary-pushing, institutions often interpret it as stress, eccentricity, or even justified assertiveness—reflections of a social norm that grants men greater empathy when they act forcefully.
By contrast, when autistic people who are women or gender-diverse set boundaries, raise their voice, or shut down in distress, those same behaviors are read as “hysterical,” “unstable,” or “defiant.” What may in fact be a protective neurological response to mistreatment is reframed as evidence of irrationality.
This is what some researchers call intra-community credibility violence: identical stress responses are excused in some groups while condemned in others. Even within autistic communities, these gendered expectations can warp perception—one person’s outburst is seen as understandable, another’s as pathological.
The result is a systemic asymmetry of empathy. Autistic people who happen to align with dominant gender expectations are more likely to be granted the benefit of doubt, while those outside those norms are denied recognition. The problem isn’t autism—it’s the cultural script about who is allowed to be angry, who is allowed to falter, and who must stay silent.
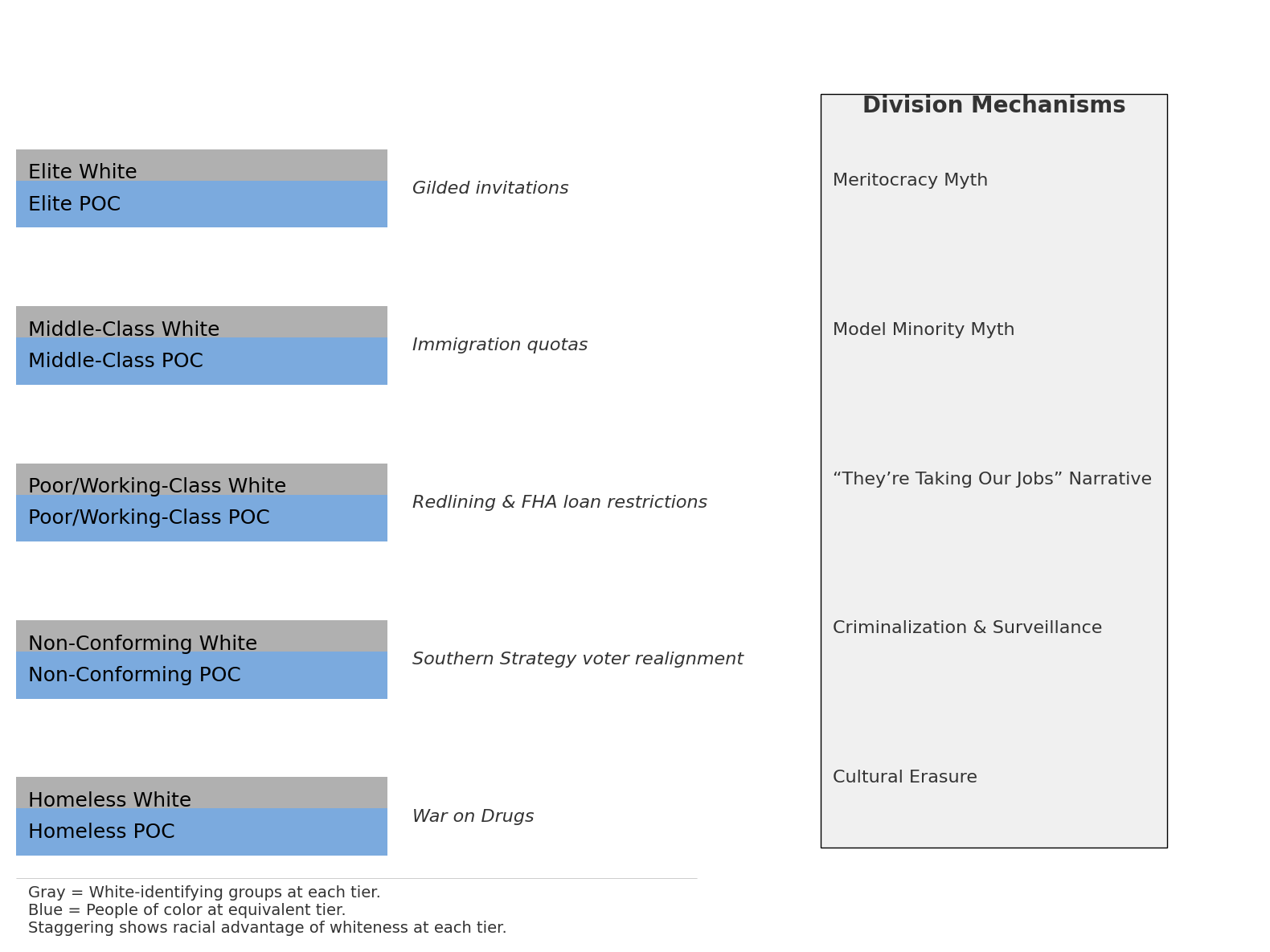
Race, Class, and Culture
Research reveals how multiple social factors compound to create credibility deficits for victims.
Racial Bias in Victim Credibility: Studies consistently show that victims of color face greater skepticism from law enforcement, juries, and institutions. Research on police responses to sexual assault found that Black women were significantly more likely to have their cases deemed “unfounded” compared to white women reporting similar circumstances. The intersection of racial stereotypes with victim-blaming creates what researchers call “gendered racism”—where women of color are simultaneously hypersexualized and deemed less credible when reporting sexual violence.
Class and Economic Status: Socioeconomic status dramatically affects whether victims are believed. Wealthy victims receive more institutional support and media sympathy, while poor victims are often blamed for their circumstances. Research shows that homeless individuals reporting assault are significantly less likely to have their cases investigated thoroughly. The assumption that poverty indicates moral failing extends to victim credibility—the thinking being that “good people” don’t end up in vulnerable situations.
Cultural Narrative Differences: Research on asylum seekers reveals how cultural differences in memory and storytelling are misinterpreted as deception, contributing to a “culture of disbelief.” Standard credibility tools ignore 88% of the world’s population, creating systematic bias against non-Western narrative patterns. Indigenous peoples face particular credibility gaps—historically portrayed as untrustworthy while the “perfect victim” template assumes white, middle-class cultural norms.
This creates a hierarchy of believability where white, wealthy victims who conform to cultural expectations receive the most institutional support, while victims with multiple marginalized identities face compounding skepticism.
The Perfect Victim Mythology
Media has created an impossible standard—the “perfect victim”—that no real person can meet. The Victorian Women’s Trust describes her: “a virgin who’s never had a drink, doesn’t post on social media, comes forward at the perfect time, and has witnesses to corroborate her story. Most importantly, she doesn’t exist.”
This mythology serves as a function: it maintains the illusion of caring about victims while ensuring almost no real victims meet the standard for believability. And if disbelief is upheld by myths of the perfect victim, breaking the pattern requires rewriting the scripts themselves.
What Actually Works
Research identifies interventions that improve institutional responses:
- Restorative Justice: Shows “considerable reductions in negative emotions” and gives victims “greater sense of control.”
- Trauma-Informed Training: Reduces secondary victimization risk in institutions working with victims.
- Institutional Courage: Commitment to truth and moral action despite short-term costs, including accountability and transparency.
- Technology Solutions: Internet-based interventions and telepsychiatry overcome geographical and financial barriers.
These reforms matter because the abstract patterns aren’t abstract at all. They determine whether someone like me is believed or broken.
Breaking the Pattern
Meaningful change requires addressing victim disbelief systemically:
- Individual Level: Recognize Just World Bias, challenge “perfect victim” mythology, understand credibility is about power, not worthiness.
- Institutional Level: Implement trauma-informed training, create transparent accountability, shift from self-protection to victim-centered approaches, measure success by victim outcomes.
- Cultural Level: Challenge victim-blaming media narratives, recognize intersectional credibility factors, support all victims regardless of “worthiness.”
The Thread Continues
My experience at Adusa reveals the predictable nature of institutional victim disbelief. Once Jim was no longer my trainer, my performance dramatically improved. My new trainer described me as competent and knowledgeable. This competence and knowledge came to good use later. When Hurricane Florence devastated the Carolinas, I was part of the team that ensured that the Eastern seaboard customers received orders and shelves stayed stocked despite system failures. I figured out how to receive the order report without WiFi and manually process hundreds of orders—a task so complex it had been automated.
My competency after Jim’s influence was removed proved the “problem employee” narrative had been false. But eight months of institutional gaslighting had done its damage. This pattern—where victims’ capabilities become evident only after harassment ends—shows how protecting perpetrators doesn’t just harm individuals; it damages organizational effectiveness.
My story wasn’t unique, it was predictable. The same biases that led colleagues to disbelieve me operate in courtrooms, police stations, schools, and HR departments worldwide. The same incentives that protected Jim protect sexual predators, workplace bullies, and those who abuse trust.
Understanding these patterns doesn’t make them less painful but makes them less mysterious. Victim disbelief isn’t a bug in our social systems—it’s a feature designed to maintain existing power structures. The thread of disbelief connecting my story to millions of others isn’t invisible, it’s been documented and analyzed for decades.
Now it’s time to cut it.
Sources for Verification
Primary Research: PMC, ScienceDirect, university research centers (Oregon, Harvard, UCLA, MIT), government agencies (Office of Justice Programs, UNODC), professional organizations.
Key Research Areas: Just World Hypothesis (Lerner, 1960s–present), Institutional Betrayal Theory (Freyd, 2008–present), Intersectionality and Victim Credibility (Crenshaw, 1989–present), Cross-cultural victimization patterns, Trauma-informed responses.
Methodology: Multi-disciplinary research spanning psychology, criminology, sociology, organizational behavior. Both qualitative and quantitative studies with cross-cultural validation and longitudinal confirmation of pattern persistence.
This analysis is based on documented research patterns across multiple independent studies conducted over eight decades.
09/14/2025